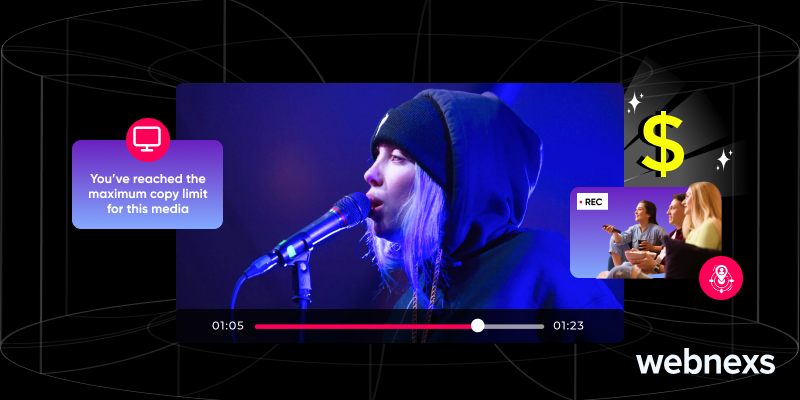
What is DRM? Digital Rights Management (DRM) is an access control technology solution that provides a way of protecting highly valuable digital intellectual property by restricting the copying, sharing and distributing of the digital files. Enterprise platforms use DRM to maintain revenue by encrypting and authentically validating users with license keys, preventing unauthorized access from mission-critical content.
According to the US Chamber of Commerce, online piracy is estimated to cost the US economy approximately $30 billion annually.
How Digital Rights Management (DRM) Works: The Technical Handshake
Digital Rights Management works as a controlled access system between content providers and end users. Every time a user presses play on a video or opens protected software a verification cycle begins in the background. This cycle checks whether the user has permission to access the content and whether their device is authorized.
At a high level DRM relies on encryption and licensing. The content is first locked using encryption algorithms then a license server decides who gets the key to unlock it. This process happens instantly but it is the foundation of modern streaming security.
This handshake ensures that content is never delivered in an open readable format unless proper authorization is confirmed. It is one of the most important mechanisms behind OTT platforms in 2026.
Read more: How does DRM work ?
DRM WORKFLOW TABLE
| Stage | Process | Description |
| 1. Upload | Content Ingestion | Video uploaded into system DRM |
| 2. Encryption | Content Protection | Content is encrypted using DRM |
| 3. License Request | User Authentication | Device requests access key |
| 4. Key Delivery | License Server | Secure key is issued |
| 5. Playback | Decryption | Video plays securely |
Encryption and Content Ingestion Processes
During ingestion the original file is broken into encrypted segments. These segments cannot be read without a decryption key. Encryption transforms readable video into secure digital fragments that appear useless without authorization.
This is where standards like AES encryption come into play. It ensures even if data is intercepted it cannot be reconstructed. Streaming platforms depend on this process to protect premium content from piracy.
The Role of License Servers and Decryption Keys
The license server acts as the decision maker. When a user requests playback the server checks subscription status device identity and region rules. If everything matches it issues a temporary decryption key.
This key is tied to the session and device. It expires after a short time which prevents reuse. This makes unauthorized sharing extremely difficult.
Looking to Secure Your Content with DRM
The Multi-DRM Ecosystem: Widevine FairPlay and PlayReady
Modern streaming platforms rely on multiple DRM systems because users access content from different devices.You will simply not have a single DRM suitable for all ecosystems, therefore multi DRM is the must-have feature.
Every DRM system is built for a unique ecosystem and guarantees interoperability across many billions of devices.
Google Widevine: Security for Android and Chrome
Widevine is widely used across Android devices and Chrome browsers. It supports different security levels depending on hardware capability. High end devices use hardware encryption for stronger protection.
Widevine is the backbone of most OTT platforms because of its scalability and global reach.
Apple FairPlay: Protecting iOS and Safari Content
FairPlay is Apple’s proprietary DRM system. It is deeply integrated into iOS macOS and Apple TV. It ensures content stays within Apple’s controlled environment.
This tight integration improves security and playback performance while limiting external access.
Microsoft PlayReady: The Windows Enterprise Standard
PlayReady is used across Windows devices smart TVs and enterprise systems. It supports offline playback and strong licensing rules which makes it ideal for business use cases.
It is widely adopted in corporate training platforms and premium video services.
DRM TYPES COMPARISON TABLE
| DRM Type | Platform Used | Best For | Security Level |
| Widevine | Android Chrome | OTT streaming | High |
| FairPlay | Apple devices | iOS streaming | High |
| PlayReady | Windows Smart TVs | Enterprise video | High |
| Marlin DRM | Set top boxes | Broadcast TV | Medium |
Why DRM is Essential for Enterprise Video Security
Digital content has emerged as a valuable business asset. DRM companies are vulnerable to piracy and revenue losses through unauthorized sharing. DRM guarantees that only paying or permitted users have access to prime content.
It also aids in enforcing contracts between studios and distributors. This makes content available based on geographical and regulatory limitations.
Copyright Compliance and Studio Distribution Requirements
Studios require strict protection rules before licensing content. DRM ensures compliance with these rules automatically.
It can enforce geo restrictions time limits and playback conditions without manual intervention. This reduces operational overhead while ensuring legal safety.
DRM vs Encryption vs Watermarking
| Feature | DRM | Encryption | Watermarking |
| Purpose | Prevent access | Protect data | Track piracy |
| Visibility | Hidden system | Hidden | Visible or invisible |
| Use Case | Streaming protection | Data security | Leak tracing |
| Control Level | High | Medium | Low |
| Example | Netflix OTT apps | Banking data | Movie leaks |
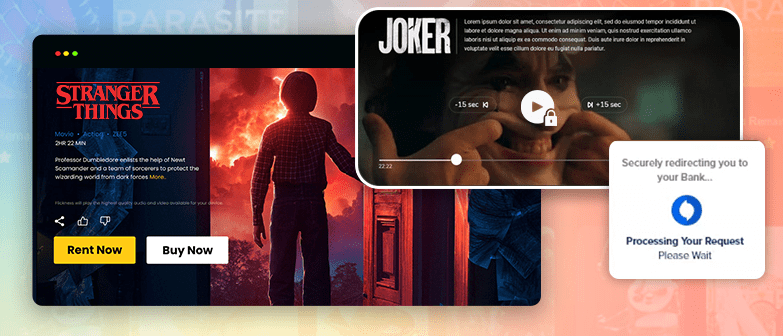
Strategic DRM Use Cases Across Modern Industries
DRM is not limited to entertainment. It is widely used across industries where digital assets need controlled access.This adaptability justifies them as a vital layer of security in the digital economy.
DRM protects sensitive content through secure distribution, from streaming platforms to corporate systems.
Media & Entertainment: Streaming Like Netflix and Disney+
Content libraries on streaming platforms are largely protected by DRM It is very fact that movies and shows could easily be replicated and disseminated without it.
DRM delivers seamless playback, locked down with ultra-tight protection across the world.
High-Security Sectors: Finance Software and E-learning
Banks use DRM to protect internal training videos and confidential materials. Software firms use it to restrict the distribution of licensed apps.
DRM is also used to safeguard proprietary courses and intellectual property on E learning platforms.
Advanced Trends in DRM Technology (2026 Update)
DRM has evolved beyond simple encryption. In 2026 it includes AI driven monitoring forensic tracking and automated piracy response systems.
These innovations in DRM render it more proactive and smarter than at any point before.
AI-Powered Piracy Detection and Real-Time Response
AI systems are constantly crawling the web for stolen material. These components audit and take automated takedown actions when pirated copies are detected.
This extends the life of illegal content and protects creators in a more efficient way.
Forensic Watermarking: Identifying the Source of Leaks
Forensic watermarking uses invisible identifiers embedded into each stream. If a leak occurs it can be traced back to the exact user or device.
This acts as a strong deterrent against internal and external piracy.
Secure VOD Content with Our Video DRM Platform
Common DRM Errors and User Troubleshooting
Even strong DRM systems can face occasional errors. Most issues come from device compatibility or expired licenses.
Understanding these issues helps users quickly restore playback.
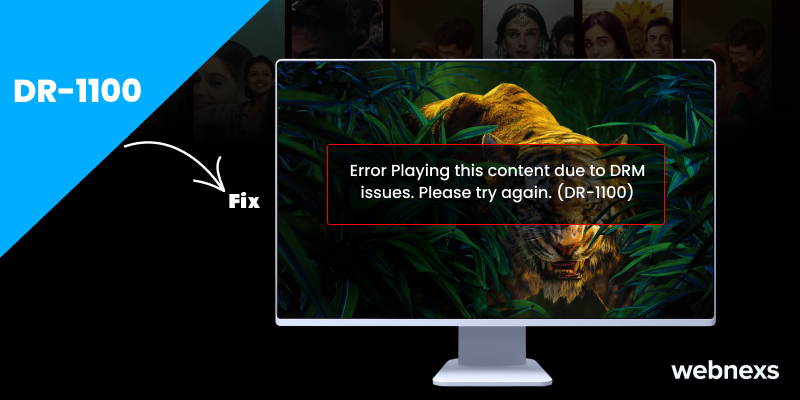
How to Fix the DR-1100 Error on Android and Smart TVs
The error DR-1100 is usually a sign of a license failure. It is often solved by restarting the app or clearing the cache.
Updating firmware also helps ensure compatibility with modern DRM systems.
Solving Device Compatibility Issues for Mac and Windows 10
That new DRM standard may not be supported by older browsers or an out-of-date operating system. Playing issues can typically be remedied by using the newest browsers like Chrome or Edge.
And of course after a system updates its versions, it returns support for Widevine and PlayReady modules.
Conclusion: Securing Your OTT Future with Webnexs
Digital Rights Management (DRM) is the central nervous system of today streaming security. ISRC prevents piracy of digital assets while allowing access for official consumers.
As OTT platform continue to grow by leaps in 2026 DRM plays a major role-facilitation of revenue protection & compliance. Without sufficient DRM, companies remain one step behind their customers; reliable implementations provide businesses with increased control over distribution and user experience overall.
Platforms like Webnexs provide advanced OTT infrastructure with multi DRM support scalable architecture and secure content delivery systems that are ready for the future of streaming.


10 Responses
Hey there, Webnexs team! I came across your article on digital rights management (DRM) and found it to be quite informative. Your article is a great resource for anyone who wants to learn more about what is DRM and how to choose the right one for their business.
The blog is an excellent resource for anyone who wants to learn more about DRM meaning and how it can benefit their business. Keep up the great work, and I look forward to seeing more informative and thought-provoking content from Webnexs in the future!
st – it’s essential to communicate with users and provide them with a clear understanding of how their data is being protected. Your article provides some valuable insights into how to build trust with users and foster a sense of transparency and accountability. This is an essential aspect of building a successful DRM strategy, and I’m glad your team emphasized it in the article.
In conclusion, I want to say that your article on what is DRM was a great read, and I learned a lot from it. Your team has done an excellent job of breaking down a complex topic into manageable chunks of information that are easy to understand. I appreciate the effort you put into researching and writing this article. Keep up the good work, and I look forward to reading more content from Webnexs in the future!
Another aspect that stood out to me in your article is the emphasis on the importance of balancing security with user experience. As you mentioned, DRM solutions can sometimes create inconvenience and frustration for users, which can lead to decreased engagement and even piracy. Therefore, it’s crucial to find a DRM solution that provides adequate protection while still offering a seamless user experience. Your article provided some great tips for achieving this balance, such as providing transparent explanations of DRM policies and giving users control over their data.
Article provides a comprehensive guide for anyone looking to implement a DRM solution for their business. I found it to be well-written, easy to understand, and informative. Thank you for sharing your knowledge and expertise with the community. I look forward to reading more articles from your team in the future.
I appreciate how you broke down the different types of DRM service and their features, as well as the factors to consider when choosing the right one for your business. It’s essential to understand the specific needs of your organization and the types of content you’re protecting to select the right DRM solution. Your article also provides valuable insights into the challenges of implementing DRM and the importance of working with experienced vendors.
Hey there! I just read your article on DRM and I must say, it was a really informative read. As someone who works with digital content, I understand the importance of protecting intellectual property and ensuring that it is not misused or distributed without permission. Your article about DRM did an excellent job of explaining the different types of DRM available and the factors that should be considered when choosing the right one for a particular use case.
Overall, I thought your article was well-written and easy to understand, even for someone who is not familiar with what is DRM. It’s clear that you have a deep understanding of this topic and have done your research to provide readers with valuable information. Thanks for sharing your knowledge and insights!
Good insight on various DRM technologies available, including watermarking, encryption, and access control. Each of these technologies has its own strengths and weaknesses, and it’s important to choose the right one based on the type of content being protected and the specific use case. Your article provided some great insights into how to evaluate different DRM solutions and make an informed decision about which one to use.